Unveiling Secrets: The Best OSINT Tools for Cyber Investigations
Harnessing the Power of Exposed Information: Your Go-To Guide for Effective OSINT in Cyber Investigations
Majd Abuleil
4 min read

Hey everyone, in today's article, I want to explain about powerful websites that can help us in our OSINT Investigations,
In every OSINT investigation, we want every detail about our target, even if this is small or big information.
For this purpose, what can be more important and useful than data that has been leaked or exposed to the public?
Yes, as you heard every year and from time to time, there will be a website or an app that suffers a data breach, exposing usernames, passwords, email addresses, and other sensitive information.
These leaked databases can be invaluable in OSINT investigations, helping us uncover hidden connections, verify identities, and track digital footprints.
To make use of this leaked data efficiently, we rely on specialized tools and platforms that aggregate and index exposed information, making it searchable and accessible for investigators. In this article, I will introduce some of the most powerful websites that assist in OSINT investigations, including platforms that help retrieve breached data, analyze online footprints, and gather intelligence from public sources.
Let’s dive in and explore these essential OSINT tools:
Have I Been Pwned [HIBP] :
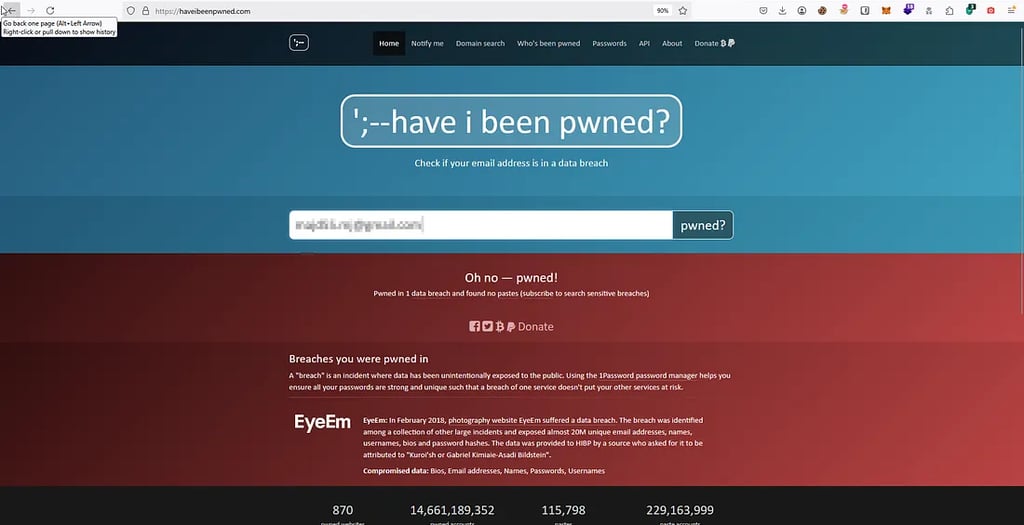
This website allows users to check if their email address or phone number has been compromised in data breaches. It serves as a resource to assess potential risks to personal information by searching through a database of leaked accounts.
As we see in the image, we can type any email, username, password, or even a phone number to check if our information has been leaked and go through a data breach database. Not just our information, but also our OSINT target’s data, allowing us to see if any of their information has been exposed in a breach.
After we check if the target or our information has breached, data or not we can go and check this on 3 other websites to search for breached data and even to see the data that has been breached even if it is a password, phone number, or username
DEHASHED:
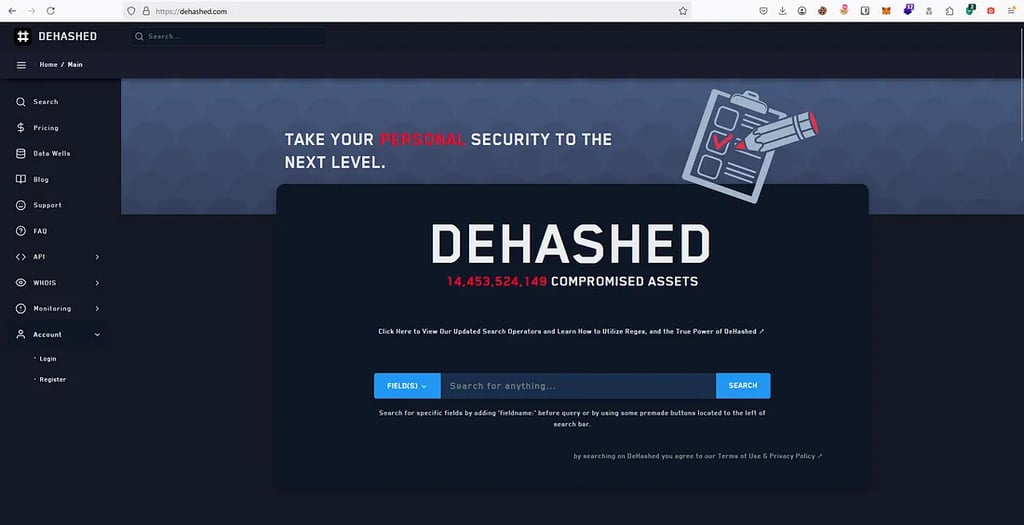
An advanced search engine designed for cybersecurity professionals, OSINT investigators, and ethical hackers to search for compromised credentials, leaked databases, and exposed personal information from data breaches. It provides access to a vast collection of breached data, allowing users to search by:
Emails, Usernames, Passwords (hashed & plaintext), Phone Numbers & IP Addresses.
On this website and search engine, users can enter any data to check if it has been involved in a breach, and see the data.
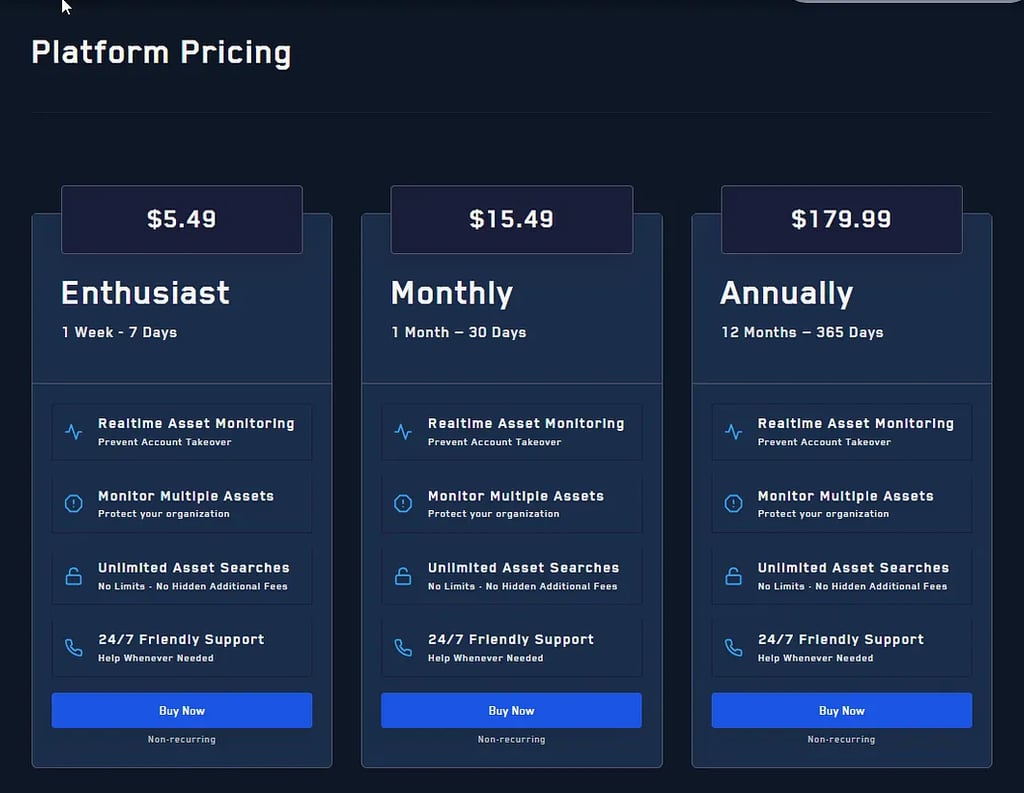
To see the breached data, like the password, you need to subscribe to this website.
After I subscribed, I went back to the search engine typed an email, and searched for it, and pengo there I found breach data that included the username, the name, and email & Hashed Password.
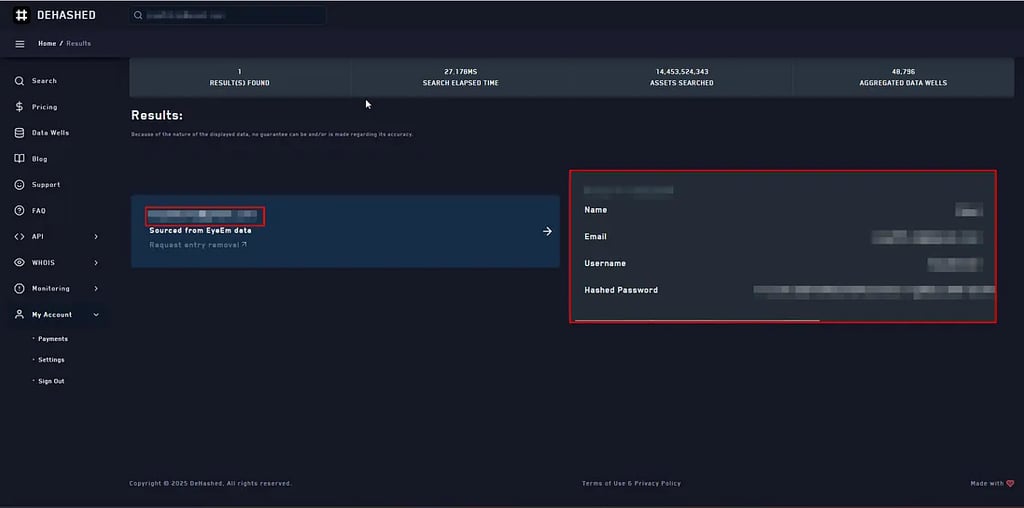
As we see in the image all the information about the email is there and we can see it.
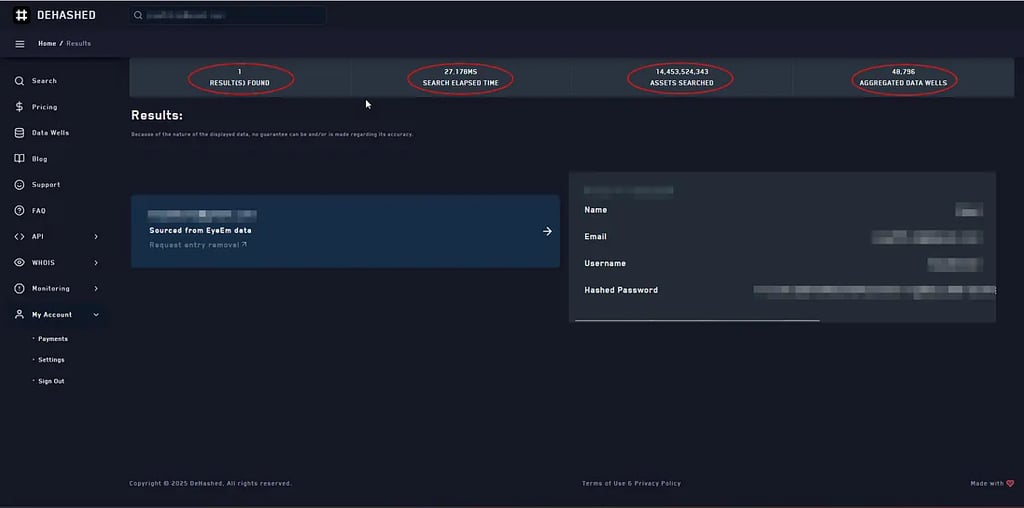
At the top of the page, we can find that this search found 1 result, and the time that takes to find it is 27.178ms and 14,453,524,343 Assets Searched & 48,796 Aggregated Data Wells.
Intelligence X:

Intelligence X operates similarly to Dehashed, functioning as a search engine and data archive that specializes in open-source intelligence (OSINT). It assists cybersecurity professionals in investigating data breaches by enabling them to search for leaked information across various platforms, including the dark web and the public web
The service of Intelligence X offers a yearly subscription for full access to its search results, including API access and premium support, while also providing limited free access with restrictions on features and data.
snusbase:
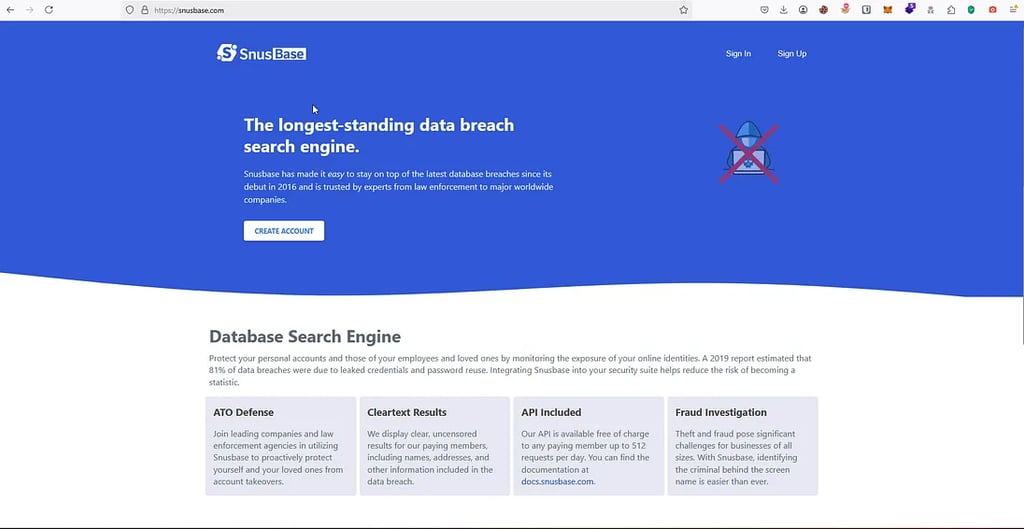
Another website that we can use to search for leaked information from data breaches.
It allows users to search for things like email addresses, usernames, and passwords that may have been exposed online.
This site is like the other website, requires a subscription for full access to its features. While there may be limited free access available, users typically need to subscribe to unlock the complete range of services, including more extensive search capabilities and additional data. The subscription model allows users to access the platform’s full database and tools for checking leaked information.